In the fast-paced digital landscape of 2025, where businesses rely heavily on technology for everything from customer interactions to supply chain management, data logs are paramount for any business operation to maintain operational integrity. Data logs, essentially chronological records of events, actions, and transactions within software systems, networks, and applications, capture critical information about what happens behind the scenes. These logs include timestamps, user actions, error messages, system performance metrics, and more, forming a digital breadcrumb trail that organizations can follow to understand their operations deeply.
The importance of data logs in business cannot be overstated. They serve as the foundation for troubleshooting issues, enhancing security, ensuring compliance, and driving informed decision-making. For instance, when a system outage occurs, logs provide the forensic evidence needed to identify root causes quickly, minimizing downtime that could cost businesses thousands per minute. In an era where cyber threats are rampant, logs act as a first line of defense by recording suspicious activities, enabling rapid response to breaches. Moreover, with regulatory frameworks like GDPR, HIPAA, and PCI DSS demanding accountability, logs help maintain audit trails that prove adherence to standards, avoiding hefty fines.
Beyond reactive measures, data logs empower proactive strategies. By analyzing log data, businesses can spot trends, optimize performance, and predict potential failures. In software development, logging is integral to debugging and iterating on code efficiently. For enterprises managing vast infrastructures, centralized logging systems aggregate this data, making it accessible for real-time monitoring and analysis. As we delve deeper, it’s clear that without robust logging practices, businesses risk operating in the dark, vulnerable to inefficiencies, security lapses, and regulatory pitfalls. This article explores why data logs are paramount, covering best practices, considerations, and real-world applications to equip any operation with the tools for success.
The Importance of Data Logs in Business
Data logs are indispensable for maintaining the health and security of business operations. At their core, they provide visibility into system behaviours, which is crucial for identifying anomalies that could signal operational disruptions or security threats. For example, on e-commerce platforms, logs track user sessions, payment transactions, and inventory changes, enabling teams to quickly detect fraud or performance bottlenecks. This visibility translates to operational efficiency, as businesses can reduce mean time to resolution (MTTR) for issues, ensuring minimal impact on revenue.
In business-critical logging, logs are not just optional; they are essential for high-stakes environments like finance or healthcare, where even minor errors can have cascading effects. Logging for business operations helps in capacity planning by revealing usage patterns, enabling scalable resource allocation. Moreover, logs facilitate root cause analysis, turning potential crises into learning opportunities. A study from 2024 highlights that organisations with effective log management experience 30% faster issue resolution, directly boosting productivity.
The audit trail importance cannot be ignored either. Audit trails, built from comprehensive logs, create an immutable record of actions, which is vital for internal audits, dispute resolution, and legal proceedings. In cases of data breaches, these trails help reconstruct events, assigning accountability and mitigating damage. For global enterprises, logs ensure transparency across distributed teams, fostering trust and collaboration. Ultimately, the importance of data logs in business lies in their ability to transform raw data into actionable insights, safeguarding operations against the uncertainties of the digital world.
Data Logging Best Practices
Adopting data logging best practices is key to maximizing the value of logs while minimizing overhead. First, implement consistent log levels—such as DEBUG, INFO, WARN, ERROR, and FATAL—to control verbosity and ensure only relevant data is captured without overwhelming storage. This practice aids in filtering noise during analysis, making troubleshooting more efficient.
Application logging best practices emphasize context-rich entries. Include unique identifiers like request IDs or user sessions in logs to correlate events across services, especially in microservices architectures. Avoid logging sensitive information, such as passwords or personal data, to prevent compliance violations and security risks. Instead, use placeholders or hashing for necessary references.
Developer logging considerations involve integrating logging early in the software development lifecycle. During coding, developers should log key decision points, exceptions, and performance metrics to facilitate debugging. Tools like ELK Stack (Elasticsearch, Logstash, Kibana) or Splunk can be employed for visualization, but the focus should be on actionable logs that answer “what, when, where, and why” for any event.

Regular reviews of logging strategies are essential. Conduct periodic audits to refine what gets logged, ensuring alignment with evolving business needs. By following these practices, businesses can turn logs into a strategic asset, enhancing reliability and reducing costs associated with unmanaged data growth.
Structured Logging for Applications
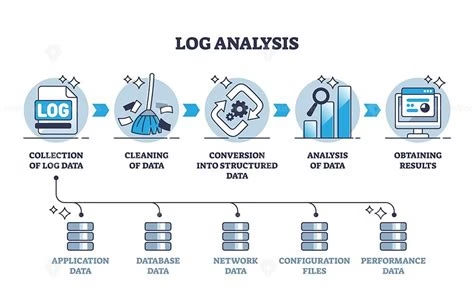
Structured logging for applications revolutionises how logs are handled by formatting them in machine-readable formats like JSON or XML, rather than plain text. This approach allows for easy parsing, searching, and aggregation, which is particularly beneficial in complex, distributed systems. For instance, a structured log might include fields like “timestamp,” “level,” “message,” and “context,” enabling automated tools to extract insights without manual effort.
In logging in software development, structured formats support better integration with monitoring tools, facilitating real-time alerts and dashboards. Developers can query logs using SQL-like syntax, speeding up diagnostics. Best practices include defining a schema for logs across teams to ensure consistency, avoiding ad-hoc fields that complicate analysis.
Structured logging also enhances scalability. As businesses grow, the volume of logs explodes; structured data compresses efficiently and integrates seamlessly with big data platforms. A 2025 report notes that enterprises using structured logging reduce analysis time by up to 50%, allowing faster iterations in development cycles.
However, implementation requires discipline. Developers must balance detail with performance, as overly verbose structured logs can impact application speed. By prioritizing structured logging, applications become more observable, directly contributing to robust business operations.
Secure Logging Practices
Secure logging practices are vital to protect log data from tampering or unauthorized access, ensuring its integrity for investigations. Start by encrypting logs both in transit and at rest, using protocols like TLS for transmission and AES for storage. Access controls, such as role-based permissions, should restrict who can view or modify logs, preventing insider threats.
Incorporate immutability by using write-once-read-many (WORM) storage, which prevents alterations post-creation. Regularly rotate log files to manage size and reduce exposure if a breach occurs. Compliance logging requirements often mandate these measures; for example, GDPR requires logs to be secure and auditable for data processing activities.
Real-time log monitoring complements security by detecting anomalies instantly. Tools like SIEM (Security Information and Event Management) systems analyze logs in real-time, triggering alerts for suspicious patterns, such as multiple failed login attempts. This proactive stance not only thwarts attacks but also supports forensic analysis post-incident.
Enterprises should integrate secure logging into their DevSecOps pipelines, scanning for vulnerabilities in logging configurations. By adhering to these practices, businesses safeguard their operational data, maintaining trust and compliance in a threat-laden environment.
Centralized Logging System and Log Management for Enterprises
A centralized logging system aggregates logs from disparate sources—servers, applications, cloud services—into a single repository, simplifying management and analysis. This centralization eliminates silos, enabling holistic views of operations and faster cross-system correlations.
Log management for enterprises involves collection, storage, analysis, and retention. Best practices include using scalable platforms like AWS CloudWatch or Google Cloud Logging for handling petabytes of data. Implement automated parsing and indexing to make logs searchable, reducing the time from issue detection to resolution.
Centralized systems support real-time monitoring, where dashboards visualize key metrics, alerting teams to thresholds like high error rates. For large-scale operations, this means predictive maintenance, identifying issues before they escalate. A 2025 best practices guide emphasizes that centralized logging can cut operational costs by 40% through efficient resource use.
Challenges include data volume; employ compression and sampling to manage it. Integration with AI-driven analytics can further enhance anomaly detection. Overall, centralized logging transforms log management into a strategic function, driving enterprise agility and resilience.
Compliance Logging Requirements and Data Log Retention Policies
Compliance logging requirements vary by industry but universally demand detailed, tamper-proof records. For financial services, SOX requires logs for financial transactions; healthcare under HIPAA mandates access logs for patient data. Businesses must log events like user logins, data modifications, and access attempts to meet these standards.
Data log retention policies dictate how long logs are kept, balancing compliance with storage costs. Regulations like PCI DSS require one-year retention for audit logs, while GDPR suggests retaining only as long as necessary. Best practices include tiered retention: short-term for operational logs (e.g., 30 days) and long-term for compliance (up to 10 years).
The audit trail importance ties into this, providing verifiable evidence for regulators. Effective policies involve automated archiving and deletion, ensuring data isn’t retained indefinitely to avoid privacy risks. Regular audits of retention practices help refine policies, aligning with business evolution.

In software development, embed compliance-aware logging from the start, using libraries that enforce standards. By prioritizing these elements, businesses not only avoid penalties but also build a culture of accountability and transparency.
Conclusion
Data logs are paramount for any business operation, serving as the backbone for security, efficiency, and compliance in 2025’s digital ecosystem. From structured logging that enhances analysis to centralized systems that enable real-time insights, adopting best practices ensures logs deliver maximum value. As threats evolve and regulations tighten, investing in robust logging strategies is not optional—it’s essential for sustainable success. Businesses that harness logs effectively will thrive, turning potential vulnerabilities into opportunities for growth and innovation.
FAQs
- What are data logs?
A.Data logs are records of events, actions, and metrics generated by systems, applications, and networks, including timestamps and details for analysis. - Why is the importance of data logs in business so critical?
A.They provide visibility for troubleshooting, security, compliance, and performance optimization, reducing downtime and risks. - What are data logging best practices?
A.Use consistent log levels, add context, avoid sensitive data, and review strategies regularly for efficiency. - How does structured logging for applications benefit businesses?
A.It formats logs for easy parsing, improving searchability and integration with monitoring tools. - What are secure logging practices?
A.Encrypt logs, implement access controls, ensure immutability, and monitor in real-time to protect against threats. - Why is real-time log monitoring important?
A.It detects anomalies instantly, enabling quick responses to issues like breaches or performance dips. - What is a centralized logging system?
A. A system that collects logs from multiple sources into one location for unified management and analysis. - What are compliance logging requirements?
A. Mandates from regulations like GDPR or HIPAA for logging specific events to ensure accountability and audits. - How do data log retention policies work?
A. They specify storage durations based on compliance needs, with tiered approaches for different log types. - What is the audit trail importance in business?
A. Audit trails from logs provide chronological records for investigations, compliance, and dispute resolution.